Postfix Encryption
Thu 12 March 2015
I've been tinkering with the encryption options in Postfix for a while. Encryption between clients and their SMTP server and between SMTP servers is necessary to protect the to, from, and subject fields, along with the rest of the header, of an email. The body of the message is also protected but it's always better to utilize PGP or S/MIME cryptography to provide end-to-end protection; encryption between clients and SMTP servers doesn't provide this.
As rolled out now, encryption between SMTP servers is opportunistic encryption and is generally not required. While doing a review of my mail log I seem to be receiving most personal mail via some encrypted circuit while much of the mail coming out of listservs, like Yahoo! Groups, is not negotiating encryption on connect. I've also noticed that some email providers actually run their incoming email through an external service, I suspect for spam control, before accepting the message into their servers. Some of these spam services don't support encryption making it difficult to protect mail in transit.
Postfix documentation is pretty decent. The project seems to document most settings but sometimes they don't actually put the entire picture together. Encryption is one of those things where a complete picture is difficult to put together just by looking at a single page of documentation.
Postfix's documentation on TLS is fairly complete. What they miss on that page, forward security, must be found else where. Until last night, I had missed that last page and now have fixed my configuration to include, what I consider, acceptable settings.
Here's what I've got:
main.cf
### TLSsmtpd_tls_security_level = maysmtpd_tls_eecdh_grade = ultratls_eecdh_strong_curve = prime256v1tls_eecdh_ultra_curve = secp384r1smtpd_tls_loglevel = 1smtpd_tls_cert_file = /etc/pki/tls/certs/mail.crtsmtpd_tls_key_file = /etc/pki/tls/private/mail.keysmtpd_tls_CAfile = /etc/pki/tls/certs/mail-bundle.crtsmtpd_tls_session_cache_timeout = 3600ssmtpd_tls_session_cache_database =btree:${queue_directory}/smtpd_scachesmtpd_tls_received_header = yessmtpd_tls_ask_ccert = yessmtpd_tls_received_header = yestls_random_source = dev:/dev/urandom#TLS Clientsmtp_tls_security_level = maysmtp_tls_eecdh_grade = ultrasmtp_tls_loglevel = 1smtp_tls_cert_file = /etc/pki/tls/certs/mail.crtsmtp_tls_key_file = /etc/pki/tls/private/mail.keysmtp_tls_CAfile = /etc/pki/tls/certs/mail-bundle.crt
master.cf
submission inet n - - - - smtpd-o smtpd_tls_security_level=encrypt-o smtpd_sasl_auth_enable=yes-o smtpd_sasl_type=dovecot-o smtpd_sasl_path=private/auth-o smtpd_sasl_security_options=noanonymous
Those familiar with setting up TLS in Apache will notice a few differences here. We haven't defined ciphers or SSL protocols. This is because this is opportunistic encryption. We're just happy if encryption happens, even using EXPORT ciphers, since the alternate is plaintext. In a more controlled setting you could define the ciphers and protocols and enforce their use. Until encryption becomes the norm on the Internet (and why shouldn't it be?) I'll have to stick with just begging for encrypted connections.
It should also be noted that client-to-SMTP server connections are forced to be encrypted in master.cf as seen in the submission portion. This was a quick and dirty way of forcing encryption on the client side while allowing opportunistic encryption on the public (port 25) side.
It should be noted that ECC keys can be used with Postfix, which forces good ciphers and protocols, but most email servers have RSA keys established so problems could arise from that. Dual keys can always be used to take advantage of both ECC and RSA.
As SSLLabs is for testing your web server's encryption settings, so is CheckTLS for checking your SMTP encryption settings. These tools are free and should be part of your regular security check of your infrastructure.
By Sparks, Category: Information Security
Tags: email / Opportunistic Encryption / postfix / SSL / TLS / Confidentiality / Encryption / Integrity /
Other articles
How to really screw up TLS
Fri 12 December 2014
I've noticed a few of my favorite websites failing with some odd error from Firefox.
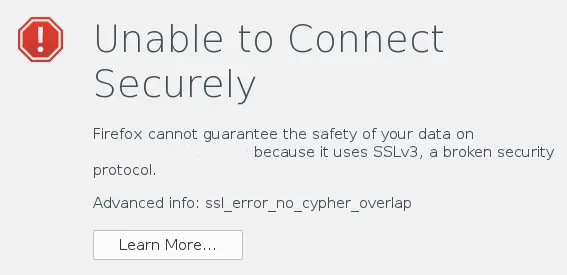 The Firefox error
message is a bit misleading. It actually has nothing to do with the
website supporting SSL 3.0 but the advanced info is spot on. The error
"ssl_error_no_cypher_overlap …
The Firefox error
message is a bit misleading. It actually has nothing to do with the
website supporting SSL 3.0 but the advanced info is spot on. The error
"ssl_error_no_cypher_overlap …
By Sparks, Category: Information Security
Continue reading …Ability to remove TLS 1.0 from httpd in CentOS 6
Thu 30 October 2014
Due to a bug in mod_ssl, the ability to remove TLS 1.0 (and only support TLS 1.1 and/or TLS 1.2) has not been available. The fix has now made it to CentOS 6 and you can now fine-tune your cryptographic protocols with ease.
Before the …
By Sparks, Category: Information Security
Continue reading …STARTTLS for SMTP
Thu 15 May 2014
Okay, I don't really mean to advocate this as a privacy solution because it is and it isn't. If you truly want privacy of your email you mustuse end-to-end encryption like PGP/GnuPG or S/MIME. That said, I think it's good to encrypt things, even ciphertext, over the …
By Sparks, Category: Information Security
Continue reading …256 Bits of Security
Thu 17 April 2014
This is an incomplete discussion of SSL/TLS authentication and encryption. This post only goes into RSA and does not discuss DHE, PFS, elliptical, or other mechanisms.
In a previous post I created an 15,360-bit RSA key and timed how long it took to create the key. Some may …
By Sparks, Category: Information Security
Continue reading …Kicking RC4 out the door
Wed 13 November 2013
I've been arguing with my web hosting company about their use of RC4. Like many enterprise networks they aren't consistent across all their servers with respect to available ciphers and such. It appears that all customer servers support TLS_RSA_WITH_CAMELLIA_256_CBC_SHA and TLS_RSA_WITH_CAMELLIA …
By Sparks, Category: Information Security
Continue reading …How secure are those SSL and SSH keys anyway?
Wed 30 October 2013
Thought I'd pass along this research study, The keys to the kingdom, as I found it to be quite interesting (especially when you scan the entire Internet for your data). If you don't understand the math explanation at the beginning just continue reading as you don't need to have a …
By Sparks, Category: Information Security
Continue reading …Trusting Trusted CAs
Wed 09 October 2013
Like it or not, the basis of trust for much of the Internet is based on Certificate Authorities (CA). Companies like Verisign, GoDaddy, and GeoTrust are in the trust business. They will sell you cryptographic proof of your Internet assets (namely your domain name) that others can use to verify …